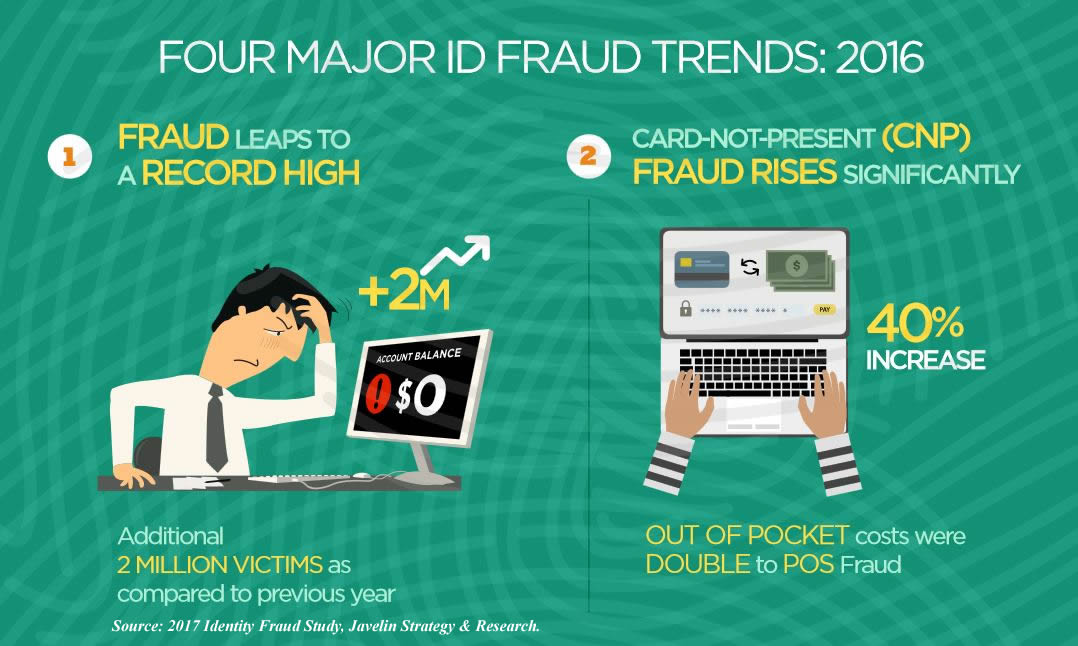
15.4 million consumers fell prey to identity fraud in 2016, the highest number of victims in the past six years. Consumers lost 16 million dollars to fraud, 6.7% higher than losses in 2015.*
In addition, as the use of EMV (chip cards) becomes more common place, identity thieves are evolving and turning their focus to online stores. While it is becoming more difficult, if not impossible, to use a counterfeit card at a physical store, a growing online market provides plenty of opportunity for abuse whenever a card does not have to be present.
A 2016 Identity Fraud Study* found 4 key trends:
- Even though the number of identity fraud victims was higher, the amount stolen was at its lowest point in six years. Over the past six years, identity thieves have stolen $112 billion. To put that into perspective, that works out to $35,600 stolen every minute. ($71,200 was stolen as I wrote this paragraph!)
- After the U.S. started requiring EMV in 2015 to reduce in-store fraud, thieves flocked to new account fraud. New account fraud occurs on an account within the first 90 days that it is open. The accounts are opened with the sole intent to commit fraud. In 2016 there was a 113% increase in new account fraud, and that now accounts for 20% of all fraud losses.
- The study noted that when a climate of distrust exists between consumers and their financial institutions, consumers are less likely to use monitoring services, alerts and credit freezes. This leaves the consumer more vulnerable to identity fraud. In these situations, a consumer’s information is used 75% longer than someone with similar protections in place. For the financial institution, this represents a 185% greater consumer expense over victims that have high trust in them.
- The study found that 18% of the identity fraud using U.S. credit cards, or $2.4 billion, was conducted outside the United States, making identity theft a global problem.
So what can you do to protect yourself as an online merchant?
Make sure you get all the information from a customer’s credit card
When taking an order or payment over the phone always ask for:
- The customer’s name exactly as it is shown on their credit card
- The full 16 digits on the card
- The verification number on the back of the card
- The cards expiration date
- Complete address (not just zip code)
- The phone number associated with the account
If someone cannot or refuses to give you full contact information, especially if the name and address seem bogus, you have every right to decline the sale. In fact, many times fraudsters will use a credit card number from a receipt they found or stole. Since the CSV code is not included on a receipt, in this case getting that number is one of your best defenses against identity fraud.
Beware of different “bill to” and “ship to” addresses
It is important to realize that this tactic is used by many credit card thieves, so be careful! Asking for a telephone number for both addresses can be especially helpful. As a matter of fact, before shipping any products you may want to run the addresses and phone numbers though a website like www.anywho.com to check for bogus billing addresses.
If you are suspicious, do some investigating
In the event that the purchase feels “off”, you should dig a little deeper. Check data fields in your forms to determine if the buyer is a real person. Verify the ZIP Code used by the customer really exists. Check the customer’s e-mail address to make sure it is formatted properly. Check for incomplete names like Mr. Smith or bogus information like as Joe Smith or John Doe for the customer’s name, or an address like 123 Main Street. Checking http://www.ussearch.com/consumer/index.jsp can give the merchant some idea of the customer’s age. Fishy contact information, coupled with the fact that the cardholder is an 80-year-old and ordering the latest video game should consequently raise your suspicions.
Be hesitant to ship extremely large orders for next-day delivery
If you receive an order that is much larger than what is normal for your business, and especially if the customer is requesting next-day delivery, proceed with caution. To be successful, credit card thieves need their sale to be approved and delivered before the identity fraud is discovered. Since they do not plan to pay for the products in the first place, many times the order will be inflated. Many developing nations use this type of scam, so if you are facing the above scenario AND the sale is international it should raise a red flag.
When in doubt, take extra steps to validate an order before you ship
If you are not sure a customer is valid, it is perfectly ok to take extra steps to prevent identity fraud. Better safe than sorry! You could ask the customer to fax you both sides of their credit card. You could also ask them to fax a copy of their driver’s license or state-issued identification. If the sale is fraudulent the thief will mostly likely give up and go elsewhere.
If you have an eCommerce store, review your orders
Most payment processing companies automatically check orders for obvious signs of fraud. Most will also allow you to set conditions yourself via your admin area i.e., requiring zip code verification. The important thing is to not rely 100% on your payment processor to pick up on fraudulent orders. You should manually review each order and look for signs of identity fraud.
Closely review and match all order totals with the totals within your payment provider control panel. If an order seems suspicious, check the IP address of the order. You can use the free tool at Hexillion (or a similar tool) to match the IP address of the computer with the address of the customer. Other steps you can take are to:
- Double check orders where the customer uses a free email account such as Hotmail, Yahoo, gmail etc.
- Double check orders that ship to a P.O. Box.
- Pay close attention to orders where the shipping address is different from the billing address.
- Avoid accepting personal checks – they can easily be stopped.
Use Real-Time Authorization
Using this method credit card information is sent to the processor for immediate approval (usually 5 seconds or less). This method ensures that the credit card has not been reported as lost or stolen and that the number is valid. The customer is still in contact with the merchant, and incorrect information can be corrected.
Let’s say the worst happens and you accept a fraudulent charge
Take immediate steps! First, call the police to report the crime. Once the police have been notified, call the cardholder’s issuing bank and ask someone to place a courtesy call to the cardholder and have them contact you. Ask the bank representative to mention that you have the shipping address for where the purchase was delivered. When the cardholder returns your call, ask them to report the crime to the police in the city where the product was shipped. You may be able to recover the stolen merchandise.
Are you using the WordPress platform for your eCommerce store?
Here are some tips for making your WordPress website more secure:
Stay current
It is very important to keep your WordPress software up-to-date. When new updates are released they include improvements, bug fixes and, but most importantly, security patches. Not updating the software will leave your website vulnerable to hacking.
Guard you back door
For the same reason listed above, plugins and themes should be kept up to date as well. Plugins and themes are “back doors” that, when not being properly updated, leave your website open to hacking, viruses and provide access to your and your customer’s personal information.
Clean house
Delete all plugins that you are not using. It is not good enough to deactivate the plugins you are not using, especially if they are not being updated. By deleting them you are closing the back door and making your website more secure. As an added benefit, you may notice your website running a little faster!
Be choosy
Be careful when downloading plugins and themes to choose reputable repositories. WordPress.org is still the most secure website to download plugins and themes from since each are thoroughly scanned before they are admitted into the library. If you purchase a premium theme or plugins, be sure to investigate the company background and reputation.
Lock it up
Make sure your files are set to the correct/secure permissions. Folders should be set to 755 or 750, files 640 or 644, and the wp-config file to 600. If someone else uploaded your files (like a web designer) verify with them that the permissions are correct.
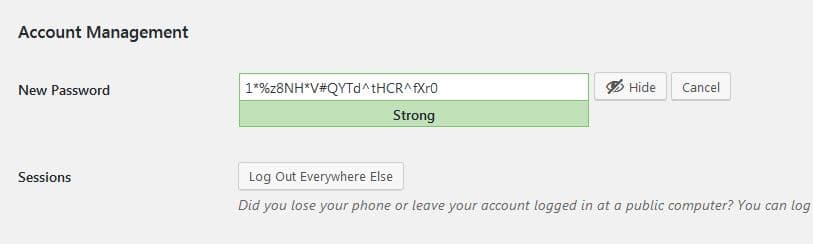
Make it difficult
Change your password frequently and make it HARD. You can use the built in WordPress password generator found inside the user tab to generate a long, ultra-secure password. Keep it in a document and simply copy and paste when needed.
Choose a good webhost
Buy the best hosting you can afford and use SSL (Secure Sockets Layer). SSL is required by most payment processors anyway. A website is only as safe as the weakest link on a shared server. Once a hacker gains access to one site on the server, they can easily infect other sites that share the same server permissions. In the end though, as WordPress.org put it, “You will need to choose from shared-hosts, managed-hosts and a number of other variations. Each host will handle security differently, but each will be consistent in that the ultimate responsibility for your installations security will fall on the website owner (not the host).”
Finally, Trust your gut
Above all, the most important thing to do is trust your instincts. If a customer does not seem completely confident about the information he or she is supplying, or you do not feel comfortable sending merchandise, simply don’t do it. Should the transaction be fraudulent, not only will you be giving your merchandise away for free, but equally important, you will give fuel to the identity fraud epidemic.
(Source: Javelin Strategy & Research, 2016 – 2017)